Focus on
The strengths of

70% improvement in detection
- Simulation of simple and complex attacks
- Engagement on any type of environment (IT, Industrial, Cloud)
- Immediate outcomes and measures of effectiveness
65% saving on your Red Team budgets
- Automatable triggering of simulations
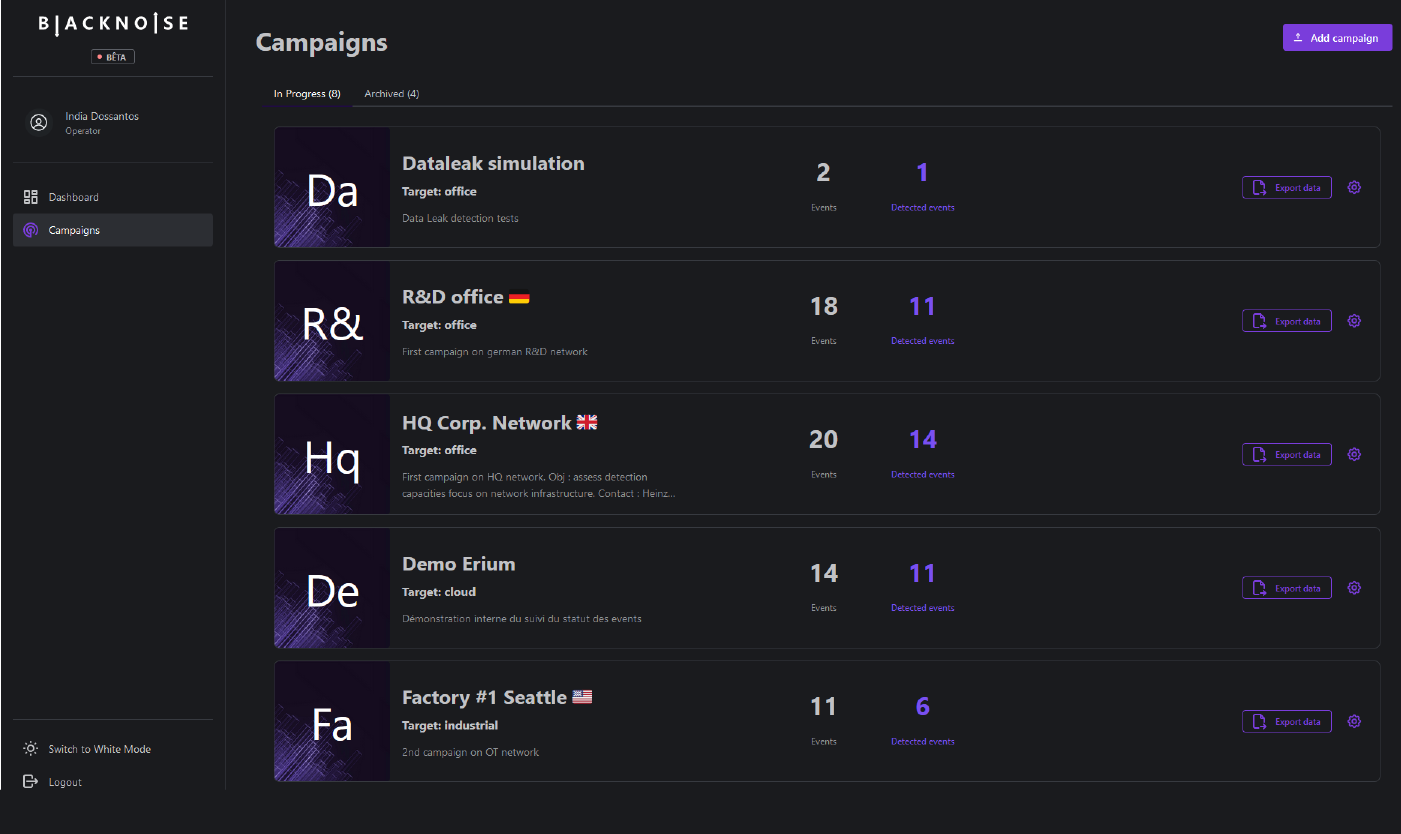
- Real time results on the BlackNoise app
- Effectiveness KPI’s based on MITRE ATT&CK and D3FEND

0 agents installed on your systems
- Accelerated deployment with no geographical constraints
- 0 integration effort, 0 persistence in your IS
- Unrivalled level of security (integrity control, multiple encryption of feeds, killswitch protocol, etc.)

Train your SOCs, CSIRTs & cyber service providers
How does it work?
BlackNoise: go beyond pentests and red teams
To avoid blind spots, upgrade your responses
- No geographical constraints
- In one-off or continuous mode
- With an application that combines all your KPI’s and results
To measure the real effectiveness of your SecOps
Detect & react faster:
- Exploitation of the vulnerability
- Deployment of autonomous exploits
- Measurement of detection times
- Reporting & technical reinforcement plan
Enabling you to defuse complex attacks
Identify and neutralise cyber attacks:
- Preparation and manual exploitation of vulnerabilities
- Network overflow attempt
- Collection of additional evidence
- Development of cyber deception strategies
To train your Cyber and IT teams in real conditions
Strengthen collective acuity:
- Cooperation between teams and Cyber
- Strengthening of response processes to advanced attacks
- Forensics & investigations into the nature of the threat
- Joint hunting operation